Encryption between end device and server
The following illustration shows how the browser on a terminal, or else the Mobile Print app, requests an https site and how the Mobile Print server responds by sending its certificate, to initiate the building of an SSL encrypted connection.
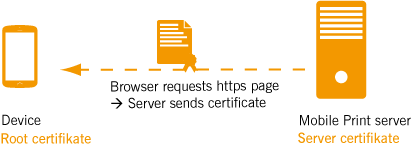
Example of the use of a server certificate
The certificate received from the server now has to be checked for trustworthiness by the mobile device. To do so, it must use the corresponding root certificate. If neither of these is located on the device (or if the specified server address does not match that written on the certificate), the user receives an error message.
Using self-generated certificates
When using self-generated certificates, such as certificates generated either with the Mobile Print server or with a separate certificate authority, take note of the following:
Note! Downloading the root certificate to the end device is necessary especially when using self-signed certificates. Officially-issued root certificates are usually already present on the devices.
Browser
If the root certificate is missing then, when opening the management console in the browser, for example, the following error message will be displayed:
„Your connection is not secure“ (Example for Firefox)
You can simply approve the unsecured connection.
However, to avoid this certificate error and to ensure a secure connection, it is recommended that a self-generated root certificate be stored in the certificate store on the terminal.
Mobile Print app
If the root certificate is missing, then secure communication via https, including a request for the user name and password is not possible. So if you use self-generated certificates, you need to distribute the root certificate to the users’ mobile devices. If the certificate concerned is generated by the Mobile Print server, the users can simply download it from the server. The download link is included in the welcome email that each user receives automatically with the user import. The users then have to save the root certificate on their mobile devices. When the EMM/MDM solution is being used, the root certificate can also be pushed to the users’ devices.